Why the Security Industry Needs a Decision Intelligence Layer
Overview
Executive Summary
The architecture of modern security systems evolved during a period when the primary challenge was detecting threats. As a result, most security environments today consist of numerous detection tools connected to various response mechanisms. However, as data volumes have increased, a structural weakness has emerged between these layers.
Detection systems generate alerts. Response systems execute actions. However, the process that connects the two, decision-making, remains largely manual. This gap is creating operational inefficiencies across security organizations worldwide. The industry increasingly requires a new architectural component: the Decision Intelligence Layer.
The Traditional Security Architecture
Most security environments follow a basic architecture composed of two primary components.
Detection Layer
Systems responsible for identifying signals that may represent threats. Examples include: • SIEM platforms • video analytics systems • intrusion detection tools • fraud monitoring systems
Response Layer
Systems responsible for executing actions in response to threats. Examples include:
• incident response platforms
• automated remediation tools
• physical dispatch systems
While these layers are essential, they do not solve the challenge of interpreting signals and determining the appropriate course of action.
The Missing Middle Layer
Between detection and response lies a critical operational function:
decision-making. This function includes tasks such as:
• evaluating risk
• prioritizing alerts
• assessing potential consequences
• determining response strategies In most organizations, these tasks rely heavily on human analysts. As environments grow more complex, manual decision processes become increasingly difficult to scale. This creates a structural gap in security architecture.
Defining the Decision Intelligence Layer
The Decision Intelligence Layer is designed to sit between detection systems and response systems. Its purpose is to transform raw security signals into actionable decision support. Core functions of this layer include:
• aggregating intelligence across security platforms
• correlating signals across domains
• prioritizing risks dynamically
• supporting human decision-making
By performing these functions, the decision intelligence layer reduces the cognitive burden placed on security analysts.
Benefits of a Decision Intelligence Layer
Introducing a decision intelligence layer can significantly improve security operations. Potential benefits include:
Improved Prioritization
Security teams can focus on the most critical risks rather than processing alerts sequentially.
Faster Incident Response
Decision support tools reduce the time required to assess threats.
Cross-Domain Visibility
Signals from cyber, physical, financial, and operational systems can be analyzed together.
Executive Risk Transparency
Security leaders can communicate risk more effectively to boards and executives.
Enabling Technologies
Several emerging technologies make the decision intelligence layer possible.
These include:
• artificial intelligence and machine learning
• advanced analytics platforms
• large-scale data integration frameworks
• graph-based intelligence models
Together, these technologies enable systems capable of synthesizing vast amounts of security data into meaningful insights.
Emerging Architectures
Some organizations are exploring architectures that integrate detection systems into unified intelligence frameworks.
These architectures function as connective layers across existing tools.
One example is the concept of a security analytics mesh (SAM), which allows security platforms to share intelligence while enabling advanced analytics and decision-support capabilities.
This approach does not replace existing security technologies. Instead, it connects them into a unified intelligence environment.
Conclusion
The security industry has invested heavily in detection and response technologies.
However, the growing complexity of modern security environments requires an additional architectural component. The Decision Intelligence Layer fills the gap between alerts and action.
By enabling faster, more informed decision-making, this layer has the potential to significantly improve the effectiveness of security operations.
Decision Velocity Problem
The Security Decision Velocity Problem
Why the Speed of Security Decisions Determines Outcomes
Author: Security 2.0, Inc.
Series: Security Decision Intelligence Initiative
Executive Summary
In security, outcomes are rarely determined by whether an event is detected.
They are determined by how quickly and effectively decisions are made after detection.
Across cybersecurity, physical security, fraud prevention, and critical infrastructure protection, organizations have invested heavily in technologies that increase visibility into their environments. These investments have dramatically improved detection capabilities.
However, detection alone does not stop incidents.
Security outcomes are determined by decision velocity — the speed at which organizations can interpret signals, prioritize threats, and initiate appropriate responses.
Today, most security architectures optimize for signal generation, not decision velocity.
The result is a growing operational challenge: security teams are receiving more alerts than ever before while their ability to convert those alerts into timely decisions has not kept pace.
This imbalance creates what can be described as the Security Decision Velocity Problem.
Solving this problem requires a new architectural approach to security systems — one that prioritizes decision support infrastructure capable of accelerating and improving the quality of security decisions.
Detection Is Not the Bottleneck
In modern security environments, the primary technical challenge is no longer detection.
Organizations have deployed extensive detection infrastructure including:
• endpoint monitoring tools
• network security platforms
• surveillance systems
• access control systems
• threat intelligence feeds
• anomaly detection algorithms
These systems are highly effective at identifying signals that may represent risk.
The bottleneck emerges after detection occurs.
When an alert is triggered, security teams must determine:
• whether the event represents a real threat
• how severe the potential impact may be
• whether immediate action is required
• which team or system should respond
These are decision-making tasks, not detection tasks.
As detection systems improve, the number of signals requiring interpretation increases. Without corresponding improvements in decision infrastructure, the result is operational overload.
The Cost of Slow Security Decisions
Security incidents often follow predictable escalation timelines.
A vulnerability becomes an exploit.
An anomaly becomes an intrusion.
A suspicious activity becomes a breach.
At each stage, organizations have opportunities to intervene.
The effectiveness of these interventions depends on how quickly decisions are made.
Slow decisions can lead to:
• delayed containment of cyber intrusions
• prolonged operational disruption
• increased financial loss
• reputational damage
• regulatory exposure
In many cases, organizations detect incidents early but fail to act quickly enough to prevent escalation.
The difference between a contained event and a major incident is often measured in minutes or hours.
Decision velocity therefore becomes a critical factor in security outcomes.
Why Decision Velocity Breaks Down
Several structural issues within modern security environments contribute to slow decision-making.
Fragmented Information
Security intelligence is distributed across multiple platforms.
Cybersecurity data, physical security telemetry, financial intelligence, and operational data often exist in separate systems.
Analysts must manually synthesize information from these environments before making decisions.
Alert Fatigue
SOC teams may receive thousands of alerts per day.
Analysts must manually triage signals to determine which require attention.
This process slows decision cycles and increases the risk of missed threats.
Context Deficiency
Many alerts lack the contextual information needed to assess risk.
For example, a login anomaly may be flagged by a cybersecurity tool, but its significance may depend on additional factors such as:
• user role
• geographic location
• associated network activity
• external threat intelligence
Without integrated context, analysts must conduct additional investigations before making decisions.
Measuring Decision Velocity
Decision velocity can be understood as the time required to move from signal detection to operational action.
This process includes several stages:
Signal generation
signal correlation
risk prioritization
decision formation
response initiation
In many organizations, the majority of time is spent in stages two through four.
Improving decision velocity therefore requires reducing the friction between signal detection and decision formation.
Decision Support as a Strategic Capability
Security leaders increasingly recognize that improving detection accuracy alone will not solve operational challenges.
Instead, organizations must develop systems that help security teams answer key operational questions faster:
• What matters most right now?
• Which threats require immediate action?
• What are the likely consequences of different response options?
These questions require systems capable of analyzing data across domains and presenting actionable insights.
This capability represents the emerging field of Security Decision Intelligence.
Toward Faster Security Decisions
Future security architectures must incorporate technologies that accelerate decision cycles.
Key capabilities may include:
• cross-system signal correlation
• dynamic risk prioritization
• predictive analytics
• scenario modeling
These functions help security teams move from reactive alert processing to proactive decision-making.
One emerging approach involves the development of integrated intelligence layers capable of synthesizing signals across multiple security systems.
This type of architecture can significantly reduce the time required to interpret signals and initiate responses.
An example of this approach is the concept of a security analytics mesh, which integrates diverse security data sources and applies advanced analytics to support operational decisions.
Conclusion
Security incidents are not prevented by detection alone.
They are prevented by fast, informed decisions.
As security environments continue to generate increasing volumes of data, the ability to make rapid, well-informed decisions will become one of the most important capabilities in modern security operations.
Organizations that improve decision velocity will gain significant advantages in risk management and operational resilience.
Achieving this improvement will require new architectural approaches focused on decision intelligence infrastructure.
From Alerts to Decisions
From Alerts to Decisions
The Security Decision Intelligence Gap
Author: Security 2.0, Inc.
Category: Security Architecture | AI | Decision Intelligence
Publication Series: Security Decision Intelligence Initiative
Executive Summary
Across the modern security landscape, organizations are not suffering from a lack of data.
They are suffering from a lack of decisions.
Over the past two decades, enterprises, governments, and critical infrastructure operators have
invested heavily in technologies designed to increase visibility into their environments. Cameras,
sensors, threat feeds, cybersecurity telemetry, access logs, and monitoring platforms now generate an
unprecedented volume of information about the state of security systems.
Yet despite this visibility, incidents continue to escalate.
See the full report: From Alerts to Decisions
Security 2.0, Inc. Awarded IDIQ Contract with U.S. Missile Defense Agency for Golden Dome Program
Company credits NVIDIA Inception and Microsoft Founders Hub support as it prepares public launch of its Security Analytics Mesh (SAM™).
Washington, D.C. — February 9, 2026
Security 2.0, Inc., an AI Consultancy, today announced it has been awarded an Indefinite Delivery / Indefinite Quantity (IDIQ) contract by the U.S. Federal Government in support of the Golden Dome initiative with the Missile Defense Agency.
The award places Security 2.0, Inc. in a highly competitive group of trusted contractors supporting one of the nation’s most critical defense missions—advancing integrated missile defense, situational awareness, and decision-support capabilities across a rapidly evolving global threat environment.
“This award represents a major milestone for Security 2.0,” said Dr. James Hall, a service-disabled veteran-owned business owner (SDVOSB), with 23 years of military service. He is the Founder and CEO of Security 2.0, Inc., and served on the founding team that initially created the Department of Homeland Security (DHS) in 2002, when the Homeland Security Act was signed into law by President George W. Bush.
“Golden Dome demands intelligence systems that move at the speed of modern threats. Our SAM™ Intelligence Layer was designed precisely for this moment, fusing data, analytics, and AI-driven insight into a unified operational picture that supports real-world decision-making.”
The SAM™ Intelligence Layer
At the core of Security 2.0’s platform is SAM™ (Security Analytics Mesh)—an AI-native modular intelligence layer purpose-built to operate across domains including defense, public safety, infrastructure protection, financial risk, and media intelligence.
Under the Golden Dome IDIQ, SAM will support government use cases ranging from intelligence discovery and signal correlation to predictive risk modeling and explainable AI outputs aligned with federal requirements.
Powered by NVIDIA and Microsoft
Security 2.0 also emphasized the importance of its participation in two globally respected innovation ecosystems:
NVIDIA Inception Program
Microsoft Founders Hub
“These programs have been instrumental in helping us scale responsibly and securely,” Hall added. “NVIDIA’s leadership in accelerated computing and AI infrastructure, alongside Microsoft’s cloud, security, and enterprise foundations, directly support the development and deployment of the SAM™ Intelligence Layer. We are deeply thankful for the technical resources, mentorship, and long-term commitment both companies provide to mission-driven innovators.”
Public Launch: February 12
Security 2.0 confirmed that February 12, 2026 will mark a major public milestone: the release of the SAM™ Intelligence Layer to broader audiences as a technology integration into the Security Television Network’s AI-Powered Search Engine for the Security Domain.
The platform will be the first of its kind—bringing professional-grade security intelligence discovery, contextual search, and explainable analytics to industry professionals, policymakers, investors, researchers, and the general public.
“This is about democratizing access to credible, structured security intelligence—without compromising trust or rigor,” Dr. Hall said. “From national defense to global markets, security impacts everyone. Our mission is to help the world discover, understand, and act on security with clarity.”
About Security 2.0, Inc.
Security 2.0, Inc. is a Mesa, AZ, U.S. based AI Consultancy security company building advanced intelligence, media, and analytics platforms at the intersection of AI, national security, and global markets. Its flagship technology includes the SAM™ Intelligence Layer and its subsidiary the Security Television Network—designed to serve government, enterprise, and public audiences alike.
Media Contact:
Press Office
Security 2.0, Inc.
Website: www.security20.com
CISOs: It’s Time to Rethink How You Discover Security Intelligence
As security leaders, your time is spent bridging technology and the boardroom, anticipating threats before they materialize, and defending critical data assets under increasing pressure. The challenge isn’t a lack of information—it's the overwhelming noise surrounding it.
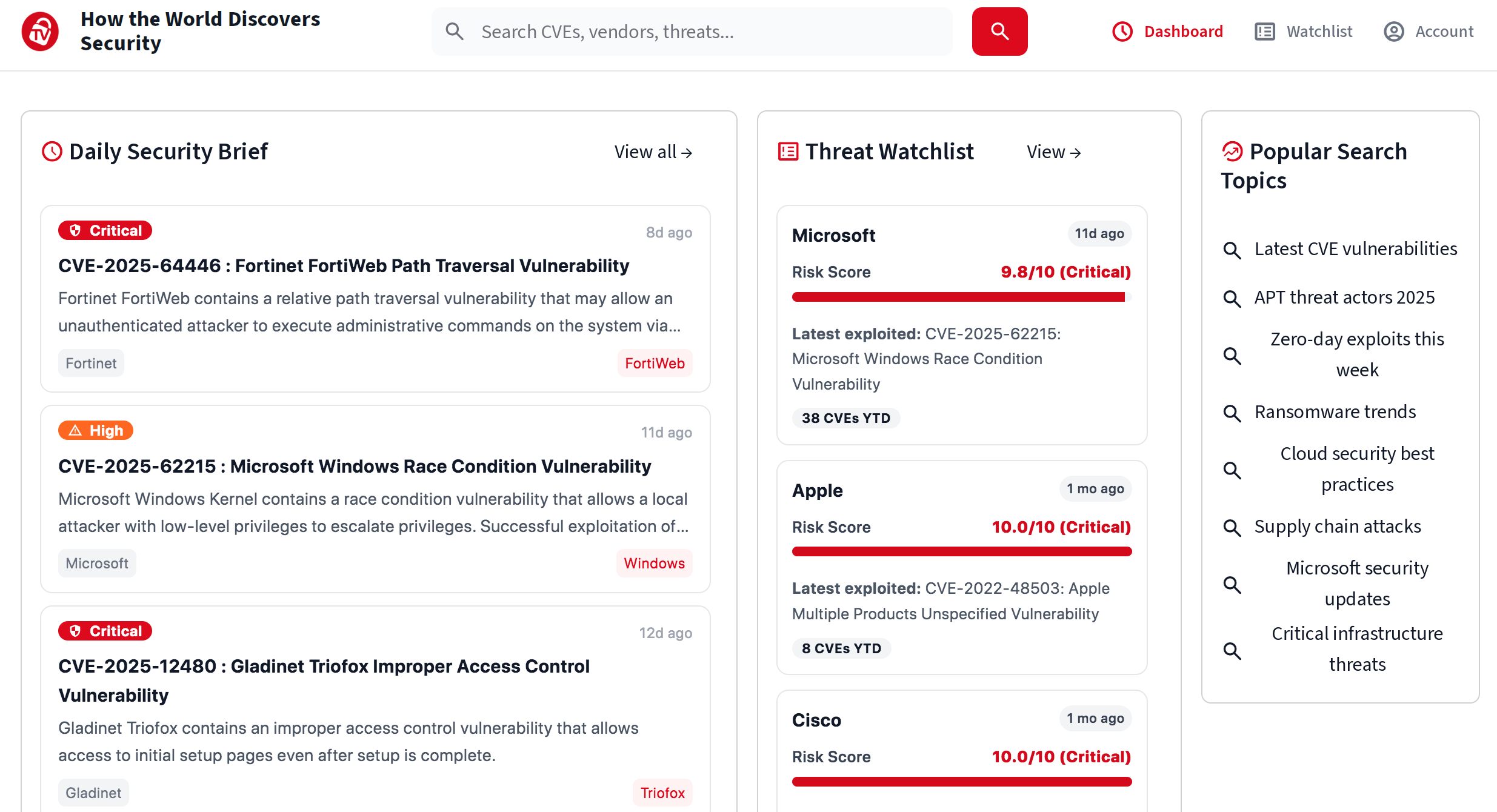
That’s why our AI-Powered Search Engine for Security was built: to give CISOs a faster, clearer, more authoritative way to conduct cybersecurity research.
Here are the Top 3 Reasons CISOs are adopting STN Search:
1️⃣ Eliminate Noise & Surface Signal Instantly
Analysts waste hours filtering irrelevant results. STN provides security-only search—curated from OSINT, government feeds, threat intelligence, regulatory updates, and enterprise-grade sources. No distractions. No clutter. Just precision.
2️⃣ Strengthen Executive Communication With Trusted, Cited Intelligence
CISOs succeed when they translate technical risks into strategic insights. STN delivers every answer with citations, timestamps, and source transparency—empowering better board reporting, risk discussions, and defensible decision-making.
3️⃣ Real-Time Awareness, From Security Headlines to Zero-Day Alerts
From CISA KEV to exploit chatter to emerging geopolitical risks, STN unifies the security universe into one intelligent interface. Faster visibility = faster action.
CISOs: If unified visibility matters to your mission, STN AI-Powered Search is built for you.
Create your own Threat Watchlist with CVEs, threats, etc.
We just launched our MVP
It's our first iteration of an AI-Powered Search Engine for the Security Domain
https://securitytv.ai
The first phase is built with one purpose: to transform how security professionals discover security. Security analysts, CISOs, and SOC teams who operate in a world drowning in noise.
Where 73% report spending more time filtering irrelevant alerts than analyzing real threats. Our MVP focuses on high-signal, authoritative public datasets such as CISA KEV, NVD, EPSS, 8-K disclosures, vendor advisories, threat feeds, and vulnerability bulletins—sources security pros trust, but don’t have time to correlate.
The search engine delivers precision search, real-time citations, and context-aware threat synthesis. It's also designed to give analysts the ability to move from question → signal → to action.
This architecture, initially optimized for high-value enterprise workflows, becomes the foundation for a much broader ecosystem: open security discovery for the public, automated watchlists for executives and investors, and eventually full-spectrum search covering cybercrime, critical infrastructure, consumer safety, and breaking global incidents.
By starting with the audience that demands the highest standard—security professionals, we created an MVP that is both commercially viable and technically extensible. We're at the beginning of solving their discovery problem now, and we're unlocking discovery for the world next.
We extend our deepest gratitude to the NVIDIA Inception Startup Program and the Microsoft for Startups Founders Hub for their unwavering support, expertise, and belief in our mission. NVIDIA’s world-class AI infrastructure, technical guidance, and global innovation community have accelerated our ability to build cutting-edge intelligence systems that power the future of security discovery.
Microsoft’s startup ecosystem, Azure resources, and mentorship have provided the foundation we need to scale securely, reliably, and globally. Together, these programs have empowered Security 2.0 and the Security Television Network to transform an ambitious vision into a world-class platform. We are honored to stand alongside two of the most influential technology leaders as we redefine how the world discovers security.
As we accelerate this next chapter, we invite visionary business partners, innovators, and industry leaders to join us in shaping the future of global security discovery. Together, we can redefine the way security is discovered, communicated, and acted upon across every sector and every corner of the world.
e-mail: info@security20.com